Guardian System
Guardian System
Complete Control Over Who Can Access What
The best security system in the world is useless if it creates a new single point of failure. Key Man Out's Guardian System provides granular control over asset access while ensuring business continuity—without compromising security.
The Three-Tier Role Hierarchy
Custodian: The Owner
Complete Control, Ultimate Responsibility
The custodian is the asset owner—the person who uploaded the secret and maintains full control over it.
Capabilities:
- Create and manage assets
- Define access rules and approval workflows
- Assign and remove guardians at any time
- Approve or deny access requests
- Receive notifications of all asset activity
- Unseal vault to access all team assets
Use Cases:
- CEO protecting company credentials
- IT manager safeguarding infrastructure keys
- Patriarch securing estate documents
- Lead developer managing API secrets
Key Principle: The custodian can always override any access decision. Final authority rests with ownership.
Gatekeeper: The Overseer
Oversight Without Access
Gatekeepers provide an additional security layer through approval authority—without gaining access to the secrets themselves.
Capabilities:
- Review and approve access requests
- Deny suspicious access attempts
- Receive notifications of access activity
- Cannot access assets - even with vault unsealed
- Cannot modify assets or assign guardians
- Can be removed by custodian at any time
Use Cases:
- Board member overseeing CEO's emergency access
- Compliance officer reviewing credential access requests
- Spouse providing oversight on business secrets
- Senior manager approving team access to sensitive systems
- Attorney monitoring access to estate documents
Key Principle: Gatekeepers provide checks and balances without creating insider threats. They can prevent unauthorized access but can't become unauthorized accessors themselves.
Successor: The Contingency Plan
Access When Custodian Cannot Respond
Successors are your business continuity plan—the people who can access assets when the custodian is unavailable.
Capabilities:
- Request access to specific assets
- Access approved assets after approval workflow completes
- Receive approved asset contents via secure access
- Cannot approve their own requests - requires custodian or gatekeeper
- Cannot modify assets or assign guardians
- Can be removed by custodian at any time
Use Cases:
- CTO accessing CEO's infrastructure credentials during emergency
- Backup administrator retrieving system passwords
- Business partner accessing contracts during owner's absence
- Adult children accessing estate documents
- Deputy manager retrieving client credentials
Key Principle: Successors ensure continuity without creating permanent exposure. Access is temporary, logged, and requires approval.
Visual Hierarchy
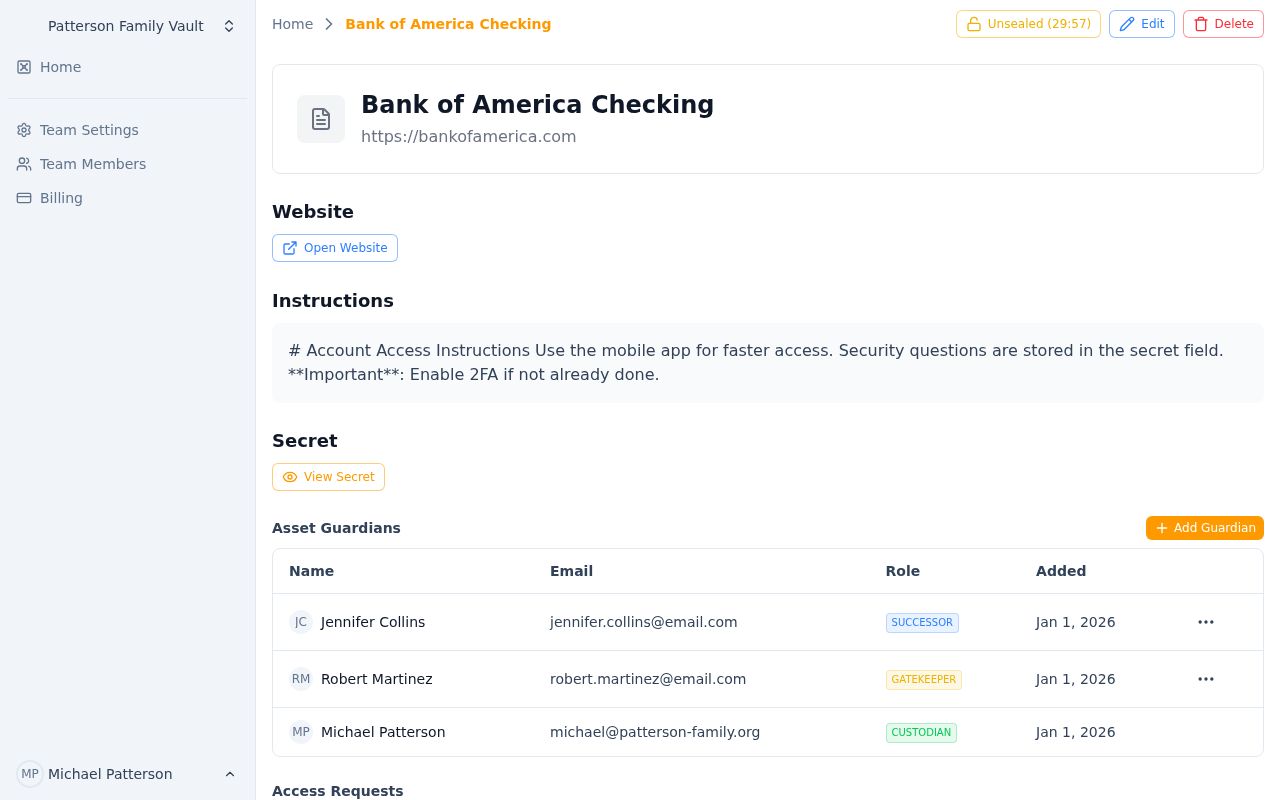 The three-tier guardian system: Custodian, Gatekeeper, and Successor
The three-tier guardian system: Custodian, Gatekeeper, and Successor
┌─────────────────────────────────────────┐
│ CUSTODIAN (Owner) │
│ • Full control over asset │
│ • Can access anytime (when unsealed) │
│ • Assigns all guardians │
│ • Final approval authority │
└─────────────────┬───────────────────────┘
│
┌────────┴────────┐
│ │
┌────────▼──────┐ ┌──────▼────────┐
│ GATEKEEPER │ │ SUCCESSOR │
│ (Overseer) │ │ (Continuity) │
├───────────────┤ ├───────────────┤
│ ✓ Approve │ │ ✓ Request │
│ ✓ Deny │ │ ✓ Access │
│ ✓ Monitor │ │ (approved) │
│ ✗ Access │ │ ✗ Approve own │
│ ✗ Modify │ │ ✗ Modify │
└───────────────┘ └───────────────┘
Guardian Assignment Scenarios
Scenario 1: Startup Infrastructure Access
Asset: Production AWS Root Credentials
Guardians:
- Custodian: CTO (owner of credentials)
- Gatekeepers: CEO, Board Member (oversight without technical access)
- Successors: Senior DevOps Engineer, Backup CTO
Workflow: If CTO is unreachable, DevOps Engineer requests access. CEO must approve (gets alert). Access granted for 24 hours, fully logged, CTO notified.
Benefit: Production stays running even if CTO is unavailable, but CEO maintains business oversight and can deny suspicious requests.
Scenario 2: Estate Planning
Asset: Bank Account Credentials and Will
Guardians:
- Custodian: Parent (asset owner)
- Gatekeepers: Attorney, Trusted Friend (ensure proper access)
- Successors: Adult Children
Workflow: After parent's incapacitation, children request access. Attorney reviews request and approves after verifying circumstances. Children receive time-limited access to coordinate estate matters.
Benefit: Assets remain protected during parent's lifetime but accessible to heirs when needed, with professional oversight to prevent premature or inappropriate access.
Scenario 3: Client Account Management
Asset: High-Value Client Contract and Credentials
Guardians:
- Custodian: Account Manager (relationship owner)
- Gatekeepers: Sales Director, Compliance Officer (business + legal oversight)
- Successors: Backup Account Manager, Regional Manager
Workflow: Account Manager on medical leave. Backup requests access to continue client service. Sales Director approves after confirming business need. Compliance Officer receives notification. Access granted for duration of leave.
Benefit: Client service continues uninterrupted while maintaining proper oversight and documentation for audit purposes.
Scenario 4: Multi-Tier Approval for Critical Secrets
Asset: Domain Registrar Master Account
Guardians:
- Custodian: VP of Engineering
- Gatekeepers: CTO, CFO, Outside Board Member (three required approvals)
- Successors: Senior Engineer, IT Manager
Workflow: VP unreachable during DNS emergency. Senior Engineer requests access. All three gatekeepers must approve (prevents single-point compromise). After all approve, access granted.
Benefit: Extremely sensitive assets require consensus, preventing rogue access while ensuring emergency availability.
Flexible Guardian Management
Dynamic Assignment
Guardians can be added or removed at any time by the custodian:
- Promote team members to successor as they gain responsibility
- Add gatekeepers when oversight requirements change
- Remove guardians when employment ends or relationships change
- Adjust approval workflows as security needs evolve
Multiple Assets, Different Guardians
Each asset has independent guardian assignments:
- Development credentials: Junior team as successors
- Production credentials: Senior team only
- Financial accounts: Executive gatekeepers required
- Personal documents: Family as successors
This granularity ensures appropriate access without all-or-nothing permissions.
Guardian Removal Workflow
When a custodian removes a guardian:
- Immediate revocation of guardian role and permissions
- Email notification to removed guardian (transparency + audit trail)
- Automatic denial of pending access requests from removed guardian
- Audit log records removal reason and timestamp
- Optional replacement assignment in same action
Security Benefit: Quick response to employment termination or trust breakdown.
Benefits Over Traditional Access Control
vs. Shared Passwords
Problem: Everyone has the password = no accountability, no oversight, no security.
Key Man Out: Successors request access individually, actions logged, custodian always informed.
vs. Break-Glass Procedures
Problem: Physical safes, sealed envelopes, unclear who can access when.
Key Man Out: Digital, logged, time-limited, remotely accessible, approval-based.
vs. Full Admin Access
Problem: Giving someone admin access = giving them everything.
Key Man Out: Successors access only what they need, only after approval, only for limited time.
vs. Trust-Based Systems
Problem: "Just trust them not to access it unless needed."
Key Man Out: Gatekeepers provide verification without requiring blind trust.
Advanced Guardian Patterns
Separation of Duties
Assign different gatekeepers for different asset types:
- Financial assets: CFO + External Auditor
- Technical assets: CTO + Security Officer
- Legal assets: General Counsel + Outside Attorney
Geographic Distribution
Ensure business continuity across time zones:
- Primary Custodian: US East Coast
- Successor 1: US West Coast
- Successor 2: European Office
- Gatekeeper: Board Member (24-hour coverage)
Escalation Hierarchies
Structure successors by seniority:
- Tier 1 Successor: Direct report (can access with gatekeeper approval)
- Tier 2 Successor: Department head (requires two gatekeepers)
- Tier 3 Successor: Executive (requires all gatekeepers + time delay)
Bottom Line: The Guardian System gives you surgical control over who can access your secrets, under what conditions, with complete oversight and accountability—without creating new single points of failure.
Zero-Knowledge Encryption
Your secrets stay secret—even from us. Learn how Key Man Out's client-side encryption and zero-knowledge architecture provides military-grade security with complete privacy.
Intelligent Access Control
Match security to sensitivity with standard approval, time-delayed access, or DNS verification. Learn how Key Man Out provides flexible, intelligent access control workflows.
